In the webinar “Top 5 Third Party Risk Management Lessons Learned from the Pandemic” Brad Keller, Vice President and CSO, Shared Assessments, and Brenda Ferraro, Vice President, Third Party Risk, Prevalent, imparted their knowledge of changes in TPRM over the past year. While the title promised 5 lessons, the webinar delivered far more. Pointing to both the pandemic and the Solarwinds attack as transformative events, Keller and Ferraro touched on modifications needed to reconcile TPRM programs with the current risk landscape.
Across the wider business landscape, of companies who rolled out new technology due to COVID, 60% bypassed or expedited standard security reviews. As vendors improvised with new technologies to mobilize a remote workforce, we have less of an understanding how vendors are doing their jobs. This points to the present as being a moment of increased risk. This impacts your TPRM program and protocols: you need to explore and examine additional or new risks – even for vendors you have already assessed.
To some extent every organization experienced business disruption during the pandemic. TPRM programs and vendors alike adapted nimbly to a new reality. But, there may be some adjustments you have yet to make.
To adjust your TPRM approach in a time of heightened risk, you need to understand:
- technology used to enable vendor’s workforce
- policy and process changes used to facilitate/authorize access changes
- open/outstanding items
- workforce training for new remote workers
- Nth Party supply and source chain inventory
You should adjust to:
- focus on incident response and event management
- bring your attention to business and ecosystem resiliency
- base your key control assessment risk factors on the new working environment
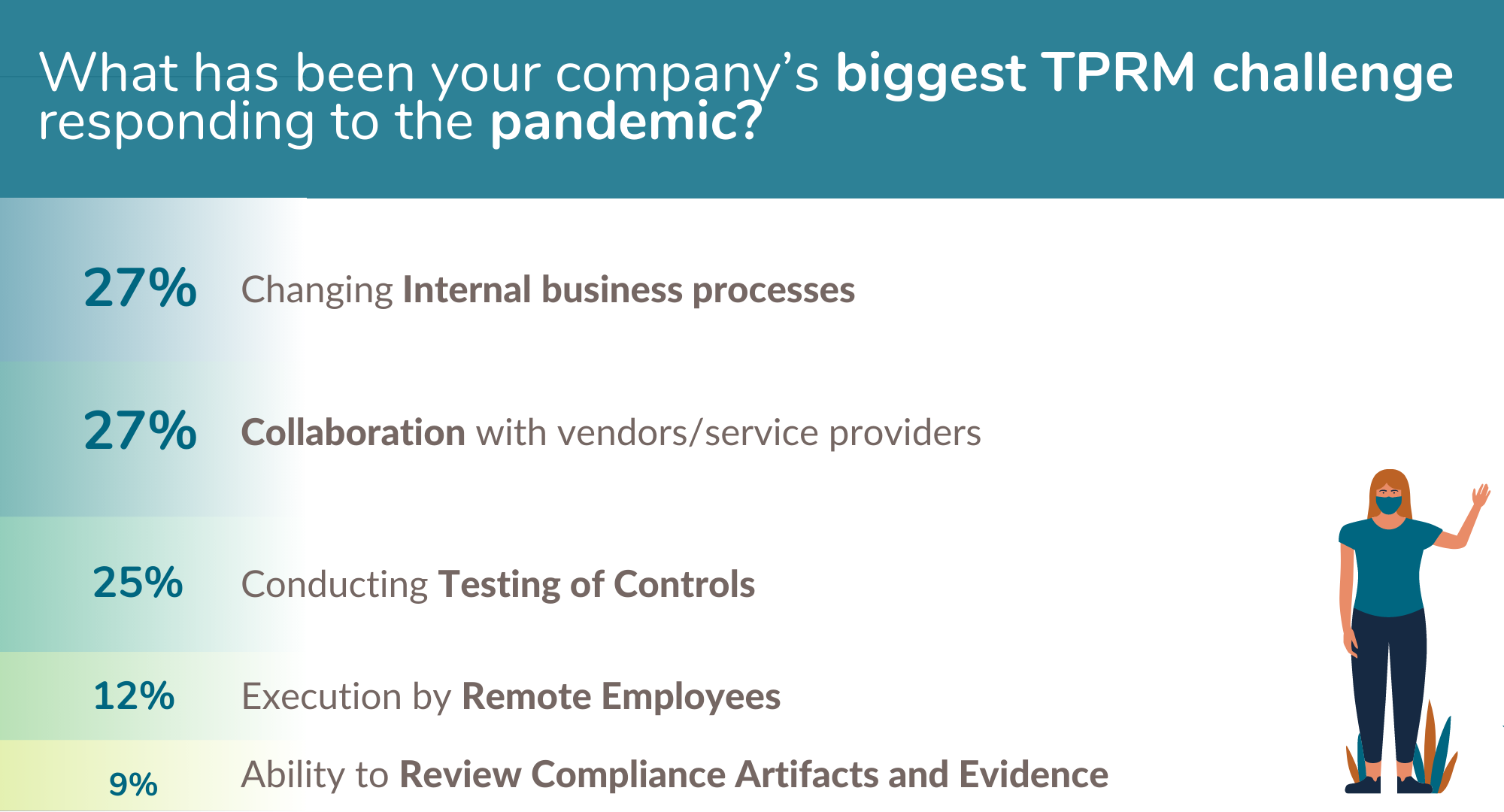
When asked “What has been your company’s biggest TPRM challenge responding to the Pandemic?” attendees answered:
- Changing our internal business processes – 27%
- Ability to review compliance artifacts and evidence – 9%
- Conducting testing of controls – 25%
- Execution by remote employees – 12%
- Collaboration with vendors/service providers – 27%
Vendor Unresponsiveness
When a vendor is unresponsive to your TPRM process, you need to look to your original vendor contract which outlines what you are authorized to do. To accomplish controls evaluations, you may need to revise your contracts to require vendors to engage with you in the business mode to which you have adapted.
Avoid the “Legal Review Conundrum”
It is wise to take a section of the contract and write it specifically to TPR and include an addendum outlining the key controls most important to you. (When you need to revise, it is simpler to look to this section rather than searching through the entire contract.) You need to build a strong relationship with the contracting arm of your organization and establish a means and regular cadence of working with this group.
Realigning Your TPRM Processes
In distanced world, you will need a new approach to assessment planning. You have to figure out how to virtually present data once examined in-person. What platform will you use? What data will be included? How many people can access the platform? Consider these factors:
- Identify technology necessary to execute new assessment processes including collaboration platforms and assurance portals
- Establish and define security protocols
- Establish and define user requirements
- Understand business and vendor association with the platform
It is most effective to repurpose content and to use contextual based machine learning. With these solutions, ongoing assessment adoption can happen (rather than just periodic). (For more detail on virtual assessments, see this blogpost.)
Define Online Protocols
To protect confidential information consider adding to all virtual data:
- Terms and Conditions for access, watermarks, footers for dissemination rules
- Limits to printing of information and use watermarks if printed
- Way to prevent documents from being downloaded from online data rooms
- Rules and exceptions for screen capture technology
Policy Management Changes
Governance and adjusting or adapting internal controls and TPRM foundation might be a bigger challenge than first realized. The majority of webinar attendees had not performed a review to determine how governance structure has been impacted by the need to conduct virtual assessments. It is wise to:
- Review current policies
- Open Exceptions for third parties that require on-site assessments
- Review current requirements or standards needing adjustments (e.g. offshore vendor standards)
- Identify and approve compensating policy or procedures
- Exception Handling
Increased Importance of Continuous Monitoring
You should use continuous monitoring across your sourcing and outsourcing chain management. As regulators request that you assess all third parties, continuous monitoring can give you the threat intelligence you need to help you prioritize where to start, whether you have 100 or 10,000 vendors. Continuous monitoring can also trigger reassessments or an instant response when needed (e.g. Solarwinds).
For the full recording of this webinar, see our on-demand webinars page.